Online Activity Documentation About Diehdfpem and Alerts Logs
Online activity documentation for Diehdfpem and alerts logs provides a centralized, auditable trail of user actions, system events, and security incidents. The framework emphasizes consistent schemas, immutable records, and standardized metadata to support fast cross-querying and lineage tracking. It underpins proactive defense, incident narratives, and governance across heterogeneous environments. The discussion will reveal practical templates, risk-points, and next steps that keep the investigation and compliance story coherent as environments evolve.
What Online Activity Docs and Alerts Logs Are For
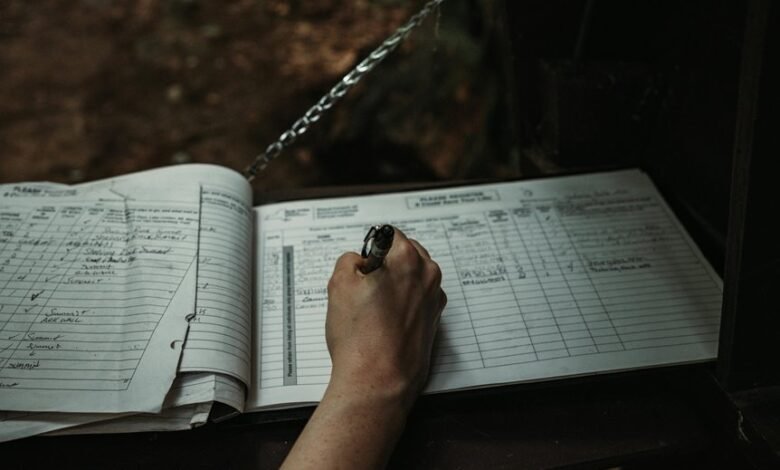
Online activity documents and alerts logs serve to capture and timestamp user actions, system events, and security-related incidents in a centralized, auditable record.
This framework supports Diaries governance by preserving narrative breadcrumbs and institutional memory.
It also enables Alerts triage, prioritizing responses, and allocating resources efficiently while maintaining autonomy.
Data integrity underpins compliance, accountability, and proactive defense across environments.
What to Log: Essential Events for Diehdfpem Environments
What to log in Diehdfpem environments centers on capturing events that directly affect security posture, compliance, and operational integrity. The essential logs cover authentication attempts, privilege changes, configuration modifications, access to sensitive data, and anomalous activity. Maintains diehdfpem governance alignment, supports audit trails, and informs incident response. An effective alerting cadence enables timely, disciplined detection and remediation. Continuous, minimal, verifiable evidence.
Structuring Records for Searchable Incident Histories
The approach emphasizes consistent schema, immutable event logs, and standardized fields for diehdfpem governance and alerting metadata.
Metadata schemas enable rapid cross-querying, audit trails, and lineage tracking, ensuring transparent incident narratives while preserving privacy, scalability, and interoperability across heterogeneous systems.
Templates, Pitfalls, and Practical Next Steps
The discussion emphasizes security audits and uptime monitoring as core controls, clarifying responsibilities, and ensuring lightweight, auditable changes.
Clear metrics enable proactive risk management and durable, autonomous operations.
Conclusion
In the quiet hum of servers, online activity documentation and alerts logs form a lighthouse for Diehdfpem environments. They carve immutable, timestamped trails through complexity, enabling rapid cross-querying and trustworthy incident narratives. By harmonizing schemas and metadata, they convert scattered events into coherent, audit-ready chronicles. The result is a precise map through governance, security, and compliance—where every action echoes in verifiable evidence, guiding stakeholders with clarity amid the fog of operation and risk.





